In the world of cybersecurity, the loudest sounds are often the ones you don’t hear. Before an ethical hacker can secure a perimeter or an adversary can exploit a flaw, they must conduct a digital stakeout. This process, known as active reconnaissance, is the art of “knocking” on a network’s doors to see who answers, which entries are bolted shut, and which have been left precariously ajar.
These field notes, gathered from a deep-dive investigation into active reconnaissance tools, expose how the most basic protocols remain the most revealing. By moving beyond simple lab walkthroughs, we can see how tools like Ping, Traceroute, and Netcat provide a high-definition map of a target’s vulnerabilities.
Tryhackme Questions/answers about this room is here
1. Your Browser is a Secret Master Key
One of the most overlooked tools in a recon specialist’s kit is the standard web browser. While most users see a webpage as a polished interface, the Web Developer Tools (accessible via Ctrl + Shift + I) allow an investigator to peel back the skin of a site’s logic.
During reconnaissance, these tools reveal how a site connects via TCP port 80 (HTTP) or TCP port 443 (HTTPS). More critically, they expose the “Security through Obscurity” fallacy. Developers frequently leave sensitive structural information in client-side scripts, assuming average users won’t look under the hood. In our investigation, inspecting a file named script.js through the Debugger tab immediately exposed the site’s internal logic, including the exact count of eight questions programmed into the page.
To move from amateur to pro, your toolkit should include:
- FoxyProxy: For seamless proxy management.
- User-Agent Switcher and Manager: To spoof your identity and see how the server responds to different devices.
- Wappalyzer: To instantly identify the frameworks and tech stacks powering a target.
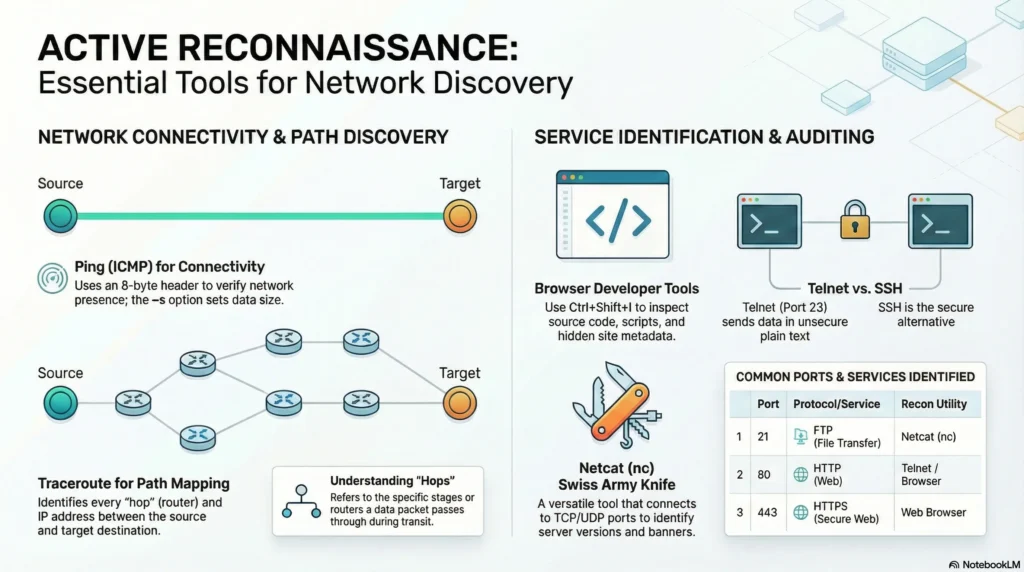
2. The Humble Ping is More Than a Heartbeat
Ping is often dismissed as a basic “up or down” check, but it is a nuanced diagnostic probe. The process follows a classic “ping-pong” analogy:
“We send a ping (a request) to a system, hoping to receive a pong (a response) to verify if we have network connectivity.”
Beyond simple connectivity—demonstrated by a 100% success rate when issuing ping -c 10—advanced configurations allow for stealth and depth. The -s flag is particularly potent, allowing an operator to set the exact size of the data carried by the ICMP echo request.
Technically, every ping carries an 8-byte ICMP header. This is a critical metric for the modern journalist-hacker; by manipulating data sizes, an investigator can test the Maximum Transmission Unit (MTU) of a network or attempt to bypass simple filters using fragmented packets. Understanding that Windows Firewalls block these requests by default turns a “no response” from a dead end into a diagnostic clue: the host is likely alive, but the “shades” are pulled down.
3. The Path to a Server is Never a Straight Line
The journey of a packet is rarely a direct flight. Tools like traceroute (on Linux and macOS) and its Windows counterpart, tracert, reveal the “hops”—the individual routers—a packet traverses.
Our investigation highlighted the counter-intuitive, dynamic nature of the internet. Because routers use dynamic protocols to adapt to congestion or hardware failure, the map of the internet is a living, breathing entity. A path to a target like TryHackMe.com can fluctuate wildly, shifting from 14 hops to 26 hops in a single session. This reveals that the “map” is never static; it is an evolving landscape where the last router before the destination (such as IP 172.67.69.208 or 104.26.11.229) provides the final gateway into the target’s infrastructure.
4. Telnet: The Danger of “Loud” Protocols
Telnet (Teletype Network) is a relic of an era before encryption, typically operating on port 23. In a modern security context, it is a “loud” and dangerous protocol because it communicates entirely in plain text.
For a recon specialist, Telnet’s greatest value is “banner grabbing.” It is an inherently “chatty” protocol, often handing over a system’s blueprints without requiring a single password. By connecting to a web server on port 80 and issuing a manual request—GET / HTTP/1.1—the server will often blurt out its identity. In our field test, the server immediately surrendered its specific software and version: Apache 2.4.61. This is the exact data an attacker needs to find a weaponized exploit tailored to that specific build.
5. Netcat: The Cybersecurity Swiss Army Knife
If Telnet is a specialized (and noisy) tool, Netcat (nc) is the ultimate multi-tool. Its true power lies in its versatility; it supports both TCP and UDP and can function as both a client and a listener.
The efficiency of Netcat allows an investigator to pivot between protocols with a single command. While Telnet is limited by its design, Netcat can silently probe a variety of ports. For instance, connecting to port 21 (FTP) quickly surfaced a server version of 0.17.
Beyond simple version grabbing, the ability to act as a “listener” is what makes Netcat indispensable. A listener can be used to test firewall ingress or, more aggressively, to “catch” a reverse shell from a compromised system. This ability to facilitate two-way interaction makes it a foundational tool that bridges the gap between passive discovery and active engagement.
Conclusion:
Active reconnaissance proves that high-level security often fails at the most basic levels. It isn’t about high-priced AI or complex algorithms; it’s about using foundational tools like Ping, Traceroute, and Netcat to piece together a puzzle that the target didn’t even know they were showing.
In an age where organizations spend millions on high-tech AI defenses, we must ask: are we doing enough to secure the “plain text” windows we’ve left wide open? As these lessons show, the most sensitive secrets are often just a “virtual knock” away.