Sun Tzu famously noted in The Art of War, “If you know the opponent and know yourself, your victory will not be in doubt.” In the modern cybersecurity landscape, this ancient wisdom translates into a high-stakes game of digital hide-and-seek. For a researcher or red-teamer, the primary challenge is mapping an opponent’s digital presence—often a sprawling mess of “Shadow IT” and forgotten cloud assets—without alerting their Security Operations Center (SOC).
The answer lies in Passive Reconnaissance. By leveraging public records and third-party databases, we can map the digital battlefield and identify critical vulnerabilities without ever “knocking on the door” of the target’s infrastructure.
Questions/Answers of this room is here for tryhackme.
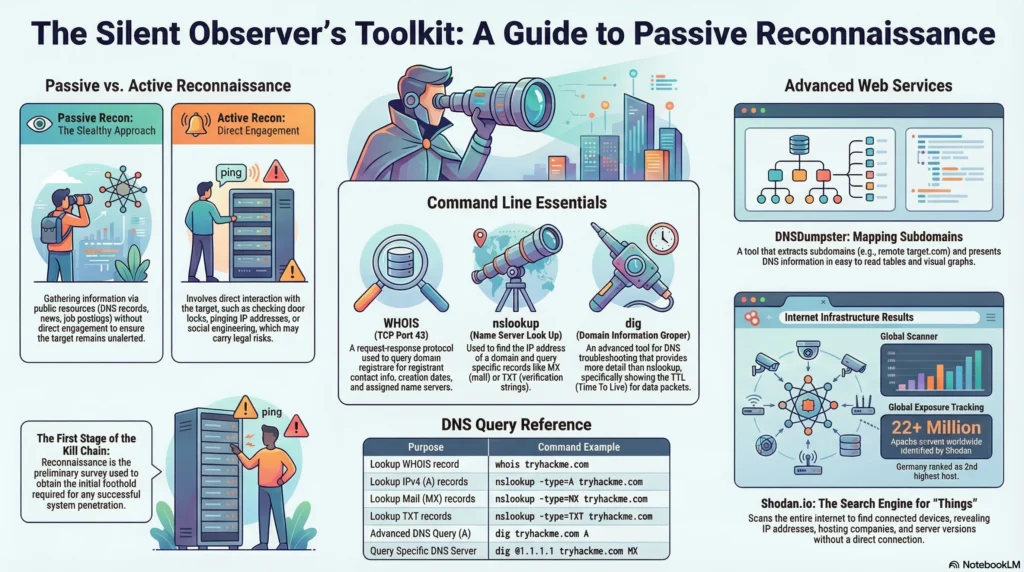
The “Doorbell” Rule: Passive vs. Active Recon
In the Unified Kill Chain, reconnaissance is the first stage of gaining an initial foothold. However, the method of recon determines whether you remain a ghost or trigger an alarm. Active reconnaissance involves direct interaction, such as checking the locks on doors or ringing a doorbell to see if anyone is home. Passive reconnaissance is the act of observing that same building through a high-powered telescope from a mile away.
| Stealth vs. Contact | Description | Examples |
| Passive Recon | Zero direct engagement with target systems; relies on publicly available resources. | Querying DNS records, examining job postings, reading news reports, or viewing public social media profiles. |
| Active Recon | Direct interaction with the target’s infrastructure. High risk of detection. | Pinging an IP, connecting via HTTP/FTP/SMTP, or social engineering an admin at a party. Note: Unauthorized active recon can lead to severe legal complications. |
1. WHOIS: Following the Digital Paper Trail
The WHOIS protocol, operating on TCP port 43, is a request-response system that queries databases maintained by domain registrars. When an organization leases a domain, they leave behind a trail of ownership data.
For a researcher, WHOIS is less about finding a home address and more about identifying social engineering vectors. While privacy services often mask registrant names, these queries frequently reveal administrative and technical email addresses. These are the primary targets for phishing campaigns.
“The information gathered can be reviewed to identify new attack surfaces, such as social engineering or technical attacks, and an attack against the admin user’s email server or DNS servers may be considered.”
2. DNS Digging: Expanding the Attack Surface
If a domain name is a digital mask, DNS records are the anatomy beneath it. Using utilities like nslookup (Name Server Look Up) and dig (Domain Information Groper), we can transform a single domain into a list of specific, targetable IP addresses.
A Senior Researcher doesn’t just look for an IP; they look for the relationships defined in different record types:
- A & AAAA Records: Maps names to IPv4 and IPv6 addresses.
- CNAME (Canonical Name): Reveals aliases, often pointing to hidden third-party infrastructure.
- MX (Mail Exchange): Identifies who handles the target’s mail. Discovering
aspmx.l.google.comsuggests a hardened Google-managed environment, whereas a private, unpatched mail server is a massive red flag for exploitation. - SOA (Start of Authority) & TXT Records: TXT records are gold mines. They often contain SPF (Sender Policy Framework) data that reveals third-party relationships with services like Chargebee or Google, effectively mapping the target’s supply chain.
dig provides a further advantage over nslookup by providing Time to Live (TTL) data. This information tells us how long records are cached, which is vital for timing DNS-based attacks or understanding how frequently a target updates their infrastructure.
3. DNSDumpster: Mapping the Subdomain Wilderness
Command-line tools are excellent for depth, but DNSDumpster provides breadth. It is specifically designed to hunt for “subdomains”—the forgotten wilderness of a corporate network. Organizations often harden their primary www domain but neglect “shadow” environments like staging sites or legacy dev portals.
DNSDumpster visualizes this wilderness in tables and graphs. By analyzing the results for a target, you might find a high-value subdomain like remote.tryhackme.com. Crucially, DNSDumpster can identify listening services without you ever connecting to them. For instance, discovering a subdomain running TCP port 8080 via Cloudflare allows you to prioritize that asset for further passive analysis before the target even knows you’re interested.
4. Shodan: The Search Engine for the “Internet of Things”
Shodan.io is the world’s first search engine for internet-connected devices. While Google indexes web pages, Shodan indexes everything else—from servers and routers to industrial control systems. It functions like a passive version of Nmap, scraping information from devices that are already exposed to the public internet.
The scale of Shodan provides incredible journalistic and tactical “heft.” For example, a search for Apache servers reveals over 22.5 million publicly accessible instances worldwide, with Germany ranking as the second-highest hosting country.
For the researcher, Shodan provides:
- Server Versions: Identifying specific Apache or nginx versions (e.g., nginx/1.14.0) to find known vulnerabilities.
- Geographic Context: Pinpointing exactly where a server sits physically.
- Exposed Ports: Identifying common ports like 80, 443, or the frequently overlooked 8080 and 8888.
5. The Recon Stack
The true power of passive recon lies in synthesis. A professional doesn’t use these tools in isolation; they use them as a stack to build a comprehensive profile.
The Recon Stack: Professional SOP
- Enumerate: Use DNSDumpster to find the “wilderness” subdomains (e.g.,
remote.target.com). - Resolve: Use
digornslookupto find the specific A or AAAA IP addresses for those subdomains. - Analyze: Plug those IPs into Shodan to see the server type, versioning, and exposed ports (like TCP 8080) without ever sending a single packet to the target’s network.
Conclusion
Passive reconnaissance is not just a preliminary step; it is the strategic foundation of the Unified Kill Chain. By utilizing WHOIS, DNS utilities, DNSDumpster, and Shodan, you can strip away the target’s anonymity while remaining entirely invisible. In an era where every device is connected and every record is public, information is the ultimate power.
Final Thought: In a world where your third-party integrations and staging servers are indexed by the minute, is any part of your network truly invisible?